 Did you know that viruses, ransomware, spyware, and trojans are all categorized as types of malware? Having been around for decades, these cyber threats have grown both in number and intensity. Needless to say, it pays to know how each of them works as well as how to protect your business.
Did you know that viruses, ransomware, spyware, and trojans are all categorized as types of malware? Having been around for decades, these cyber threats have grown both in number and intensity. Needless to say, it pays to know how each of them works as well as how to protect your business.
Viruses
Once created to annoy users by making small changes to their computers, like altering wallpapers, this type of malware has evolved into a malicious tool used to breach confidential data. Most of the time, viruses work by attaching themselves to .exe files in order to infect computers once the file has been opened. This can result in various issues with your computer’s operating system, at their worst, rendering your computer unusable.
To avoid these unfortunate circumstances, you should scan executable files before running them. There are plenty of antivirus software options, but we recommend choosing one that scans in real-time rather than manually.
Spyware
Unlike viruses, spyware doesn’t harm your computer, but instead, targets you. Spyware attaches itself to executable files and once opened or downloaded, will install itself, often times completely unnoticed. Once running on your computer, it can track everything you type, including passwords and other confidential information. Hackers can then use this information to access your files, emails, bank accounts, or anything else you do on your computer.
But don’t panic just yet, you can protect yourself by installing anti-spyware software, sometimes included in all-purpose “anti-malware” software. Note that most reputable antivirus software also come bundled with anti-spyware solutions.
Adware
Are you redirected to a particular page every time you start your browser? Do you get pop ups when surfing the internet? If either situation sounds familiar, you’re likely dealing with adware. Also known as Potential Unwanted Programs (PUP), adware isn’t designed to steal your data, but to get you to click on fraudulent ads. Whether you click on the ad or not, adware can significantly slow down your computer since they take up valuable bandwidth. Worse still, they’re often attached with other types of malware.
Some adware programs come packaged with legitimate software and trick you into accepting their terms of use, which make them especially difficult to remove. To eradicate adware, you’ll need a solution with specialized adware removal protocols.
Scareware
This type of malware works like adware except that it doesn’t make money by tricking you into clicking on ads, but by scaring you into buying a software you don’t need. An example is a pop up ad that tells you your computer is infected with a virus and you need to buy a certain software to eliminate it. If you fall for one of these tactics and click on the ad, you’ll be redirected to a website where you can buy the fake antivirus software.
Scareware acts more like a diversion from the other malware that often comes with it. A good antivirus solution will help scan for scareware too, but you should patch your operating systems regularly just to be safe.
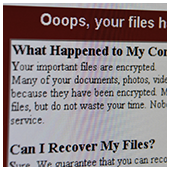
Ransomware
Ransomware has become increasingly common and hostile. It encrypts your computer files and holds them hostage until you’ve paid a fee for the decryption code. Because ransomware comes with sophisticated encryption, there aren’t many options unless you have backups of your data.
There are some tools that can protect against ransomware but we recommend that you backup your data and practice safe web browsing habits.
Worms
Similar to viruses, worms replicate themselves to widen the scope of their damage. However, worms don’t require human intervention to replicate themselves as they use security flaws to transmit from one computer to the next, making them far more dangerous than your typical virus. They often spread via email, sending emails to everyone in an infected user’s contact list, which was exactly the case with the ILOVEYOU worm that cost businesses approximately $5.5 billion worth of damage.
The easiest ways to protect your network from worms is to use a firewall to block external access to your computer network, and to be careful when clicking on unknown links in your email or unknown messages on social media.
Trojans
Usually downloaded from rogue websites, Trojans create digital backdoors that allow hackers to take control of your computer without your knowledge. They can steal your personal information, your files, or cause your computer to stop working. Sometimes hackers will use your computer as a proxy to conceal their identity or to send out spam.
To avoid trojan attacks, you should never open emails or download attachments from unknown senders. If you’re skeptical, use your antivirus software to scan every file first.
In order to keep malware at bay, you need to invest in security solutions with real-time protection and apply security best practices within your office. If you have any questions or concerns, or simply need advice on how to strengthen your business’s security, just give us a call and we’ll be happy to help.



 For many businesses, applications like Google Drive are heaven-sent. They make managing files and photos much easier and safer than manually saving them in external disk drives. That said, backing up all files remains a burden to those who have files stored on several devices and can’t seem to transfer these files onto Google Drive or any other cloud platform. Luckily, Google came up with a viable solution to this problem.
For many businesses, applications like Google Drive are heaven-sent. They make managing files and photos much easier and safer than manually saving them in external disk drives. That said, backing up all files remains a burden to those who have files stored on several devices and can’t seem to transfer these files onto Google Drive or any other cloud platform. Luckily, Google came up with a viable solution to this problem.
 The cyber community hasn’t fully recovered from the WannaCry ransomware attacks, which struck businesses and organizations in May. Now, a Petya ransomware variant named Nyetya is poised to join its ranks as one of the worst cyber attacks in history. Like WannaCry, its attackers exploited unpatched Microsoft vulnerabilities and demanded a $300 ransom in Bitcoins. But there are key differences between the two that are worth taking a look.
The cyber community hasn’t fully recovered from the WannaCry ransomware attacks, which struck businesses and organizations in May. Now, a Petya ransomware variant named Nyetya is poised to join its ranks as one of the worst cyber attacks in history. Like WannaCry, its attackers exploited unpatched Microsoft vulnerabilities and demanded a $300 ransom in Bitcoins. But there are key differences between the two that are worth taking a look.
 If you have ever received what looked like a personalized email from a huge corporation, there’s a good chance it was actually written with the help of an email automation platform. Email automation saves time and money while strengthening customer relationships, and contrary to popular belief, it is well within most SMB budgets.
If you have ever received what looked like a personalized email from a huge corporation, there’s a good chance it was actually written with the help of an email automation platform. Email automation saves time and money while strengthening customer relationships, and contrary to popular belief, it is well within most SMB budgets.
 Facebook is like a Swiss Army knife, practical and featureful. But did you know that Facebook has hundreds of built-in marketing features that 1.8 billion users worldwide are mostly oblivious to? With that in mind, here are four Facebook features you can use to boost your SMB’s social marketing efforts:
Facebook is like a Swiss Army knife, practical and featureful. But did you know that Facebook has hundreds of built-in marketing features that 1.8 billion users worldwide are mostly oblivious to? With that in mind, here are four Facebook features you can use to boost your SMB’s social marketing efforts: